The Research on Cybersecurity Risks in 5G network: Perspectives on Global strategy
The Research on Cybersecurity Risks in 5G network: Perspectives on Global strategy
I. The characteristics of 5G and cybersecurity threats
Compared to 4G, 5G adopts several new designs on the network architecture, such as software-defined networking (SDN), a baseband unit (BBU), logical disjunction, network function virtualization (NFV), and multi-access edge computing (MEC), to provide users with high-speed, low-latency and other quality services, as well as flexibility and expansibility to accommodate more emerging applications.
According to the three key usage scenarios (see Figure 1) defined by the International Telecommunication Union (ITU), enhanced mobile broadband access (eMBB) provides high-volume mobile broadband services such as AR/VR or ultra-high-definition video. Massive machine type communication (mMTC) provides large-scale IoT services. Ultra-reliability and low latency communication (uRLLC) can be used for services that require low-latency and high-reliability connections, including unmanned driving and industrial automation.
However, with 5G’s open, flexible and extensible design, as well as its coexistence with other 4G and 3G systems in the early stage of commercial operation, the cybersecurity threats facing 5G networks are more severe and diverse than the past mobile phone generations. At present, the known 5G cybersecurity threats mainly come from network functional components and connection interfaces among components, including the terminal device, access network, air interface, cloud virtualization, multi-access edge computing rental, core network, back-end/backbone network, roaming and external services, and so on.
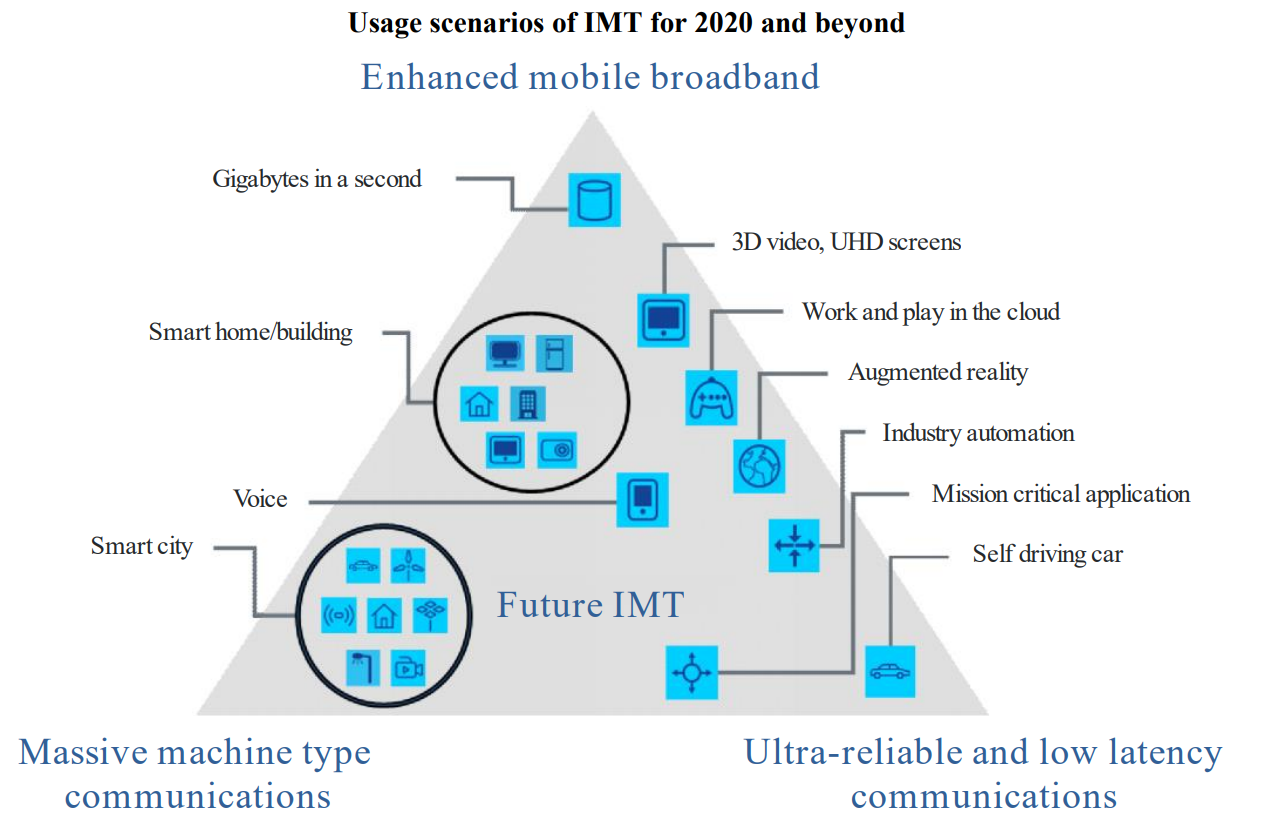
Source: ITU
Figure 1 Three key 5G scenarios by the ITU
II. Cybersecurity strategy development in major countries
5G is not only one of the critical infrastructures, but also an important foundation for pursuing a digital nation, digital economy, the industrial 4.0, and for promoting industrial transformation for upgrading. However, different scenarios require different cybersecurity protection levels, which poses great challenges to both mobile network operators and service providers.
Therefore, the construction of favorable environment for 5G development, the promotion of relevant applications and the development of innovative services and so on, have become the priority of governance in the countries around the world.
1. European Union (EU)
Then European Commission President Jean-Claude Juncker noted in 2017 that “Cyber-attacks can be more dangerous to the stability of democracies and economies than guns and tanks…Cyber-attacks know no borders and no one is immune,” indicating the EU's high priority in the cybersecurity field.
The "Digital Single Market," an important EU policy, lays the foundation for digital economy based on "cybersecurity, trust and privacy." In response to the loss of billions of euros a year in cyber attacks, the EU has taken a series of measures to safeguard and advance the development of the Digital Single Market. For the purposes of this strategy, the European Commission in 2018 came up with the policy of Resilience, Deterrence and Defence: Building strong cybersecurity for the EU,[1]with the aim of improving the level of cyber security, cyber resilience and trust in the EU, and in June 2019 passed the Cybersecurity Act [2] with two highlights described as follows:
(1) Strengthen the authority of the European Union Agency for Network and Information Security (ENISA)(see Figure 2), increase the allocation of human and financial resources to ENISA, as well as the preparation for the work items related to the cybersecurity industry, and reinforce cyber security support for EU member states.
(2) Establish the EU cybersecurity certification framework. [3]
In the European Union, where different cybersecurity certification schemes already exist, the absence of a common certification regime would increase the risk of fragmentation of the single market. For this reason, a set of technical requirements, standards and procedures are provided under this framework to assess whether information/communication products, services and processes are in compliance with security requirements.
The certification program includes product and service categories, information/communication security requirements (e.g. reference standards or technical specifications), types of assessment (e.g. self-assessment or third-party assessment), levels of security, and so on. All member states agree that certification not only facilitate cross-border business transactions, but also enable consumers to better understand the security of products and services.
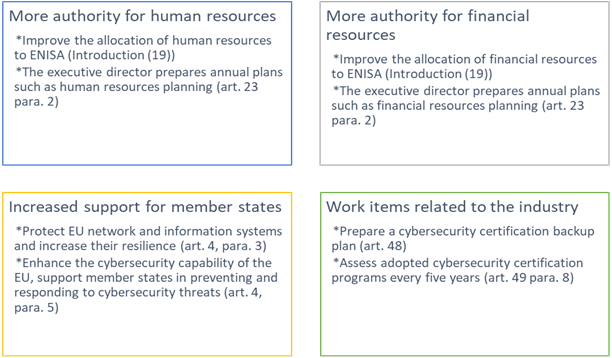
Source: Compiled from the ENISA websit
Figure 2 ENISA organization and authority strengthening
2. the United States (U.S.)
In consideration of cyber security affairs in the country, the US Department of Homeland Security (DHS) in May 2018 unveiled the "Cybersecurity Strategy,"[4] which focused on the objectives and priorities of the U.S. government in future cybersecurity protection, identifying and managing national cybersecurity risks with the overall risk management approach, and addressing security threats to the country, critical infrastructures and private enterprises, as well as preventing cybercrimes.
Then the White House in September 2018 released the National Cyber Strategy of the United States of America, [5] based on the Presidential Executive Order on Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure [6] issued in May 2017, stating the strategy and position of the United States against the threat of cyber- attacks. The strategic goal aimed to, by safeguarding cybersecurity, protect the American people, the homeland, and the American way of life, to build a secure digital economic environment, to promote American prosperity, and strengthen cooperation with partners to deter malicious cyber attackers, so as to maintain peace and security, and continue to expand U.S. influence.
The department in July 2019 published the Digital Modernization Strategy [7] to announce its national defense strategy in the digital environment, including the use of cybersecurity, AI, cloud computing, blockchain and other technologies in information security protection to create a more secure, coordinated and efficient platform and improve the security of intelligence transmission and processing.
3. Canada
Public Safety Canada in June 2018 released the National Cyber Security Strategy, [8] with the vision of a sustainable, robust cybersecurity environment, innovation and prosperity. Through international cooperation and a domestic public-private partnership, the department has been working on three goals: 1. cyber security and resilience (to reduce cybercrime and ensure Internet privacy; 2. Internet innovation (to create a friendly environment for the development of cybersecurity startups); 3. government leadership and cooperation (to transfer government-owned cybersecurity knowledge to the private sector and set up a cybersecurity governance framework).
The Canadian government also attaches great importance to critical infrastructure. In May 2018, the National Cross Sector Forum 2018-2020 Action Plan for Critical Infrastructure [9] was unveiled to facilitate information sharing between public and private partners through sharing and protecting intelligence, and implementing a full risk management approach. Moreover, Public Safety Canada in April 2019 issued a report called Enhancing Canada’s Critical Infrastructure Resilience to Insider Risk, which provided guidelines and suggestions for action on internal risks in critical infrastructure organizations.[10]
4. Singapore
The government of Singapore in 2018 promulgated the Cybersecurity Act, [11] which aimed to fulfill the vision of a Smart Nation by enacting and putting into effect cybersecurity regulations to achieve the goal of a resilient infrastructure and a more secure cyberspace, and to strengthen the protection of critical information infrastructure against cyber-attacks. The Cyber Security Agency of Singapore (CSA) was given the authority to prevent and respond to cybersecurity threats, and to set up a system for sharing security information, as well as a light-touch licensing system for cybersecurity service providers.[12]
The Government of Singapore has appointed a Commissioner of Cybersecurity responsible for promoting domestic cybersecurity policy. To safeguard Singaporeans from cybersecurity threats, [13] the government particularly laid down cybersecurity threat or incident response provisions in Chapter 4 of the Cybersecurity Act to empower the Commissioner of Cybersecurity to investigate cybersecurity threats and incidents, such as requiring the parties to the incidents to present statements in person or in writing, producing documents or provide information and so on.[14]
5. Australia
The Australian government in 2016 proposed a four-year "Australia's Cyber Security Strategy,"[15] which was expected to invest more than 230 million Australian dollars to strengthen Australia's cyber security capability and complete the following five aspects: national cyber partnership, strong cyber defenses, global responsibility and influence, growth and innovation, and a cyber smart nation.
As for the global responsibility and influence, the Australian government in 2017 announced the "Australia's International Cyber Engagement Strategy."[16] which aims to strengthen digital trade, to improve cybersecurity and to response to cybercrime through international cooperation; encourage innovative cybersecurity solutions; provide security advice and best practices, such as Essential Eight strategies[17] to mitigate cyber-attacks; establish the Pacific Cyber Security Operational Network (PaCSON) [18] with neighboring countries to develop regional cybersecurity capabilities; and advance the development of Australia's cybersecurity industry, nurture startups and attract foreign investment.
III. Cybersecurity strategy to promote 5G in Taiwan
Since President Tsai Ing-wen took office in 2016, she declared that cybersecurity is directly linked to national security. In 2017, the Department of Cyber Security (DCS) under the Executive Yuan issued "National Cybersecurity Development Plan (2017-2020)," and in 2018 the "Cybersecurity Industry Development Action Plan (2018-2025)," in order to enhance the independence of Taiwan's cybersecurity industry, consolidate the nation’s cybersecurity defense line, improve its innovative thinking of cyber security, and further promote it to the international market.
To develop a favorable environment to promote 5G, the Executive Yuan on May 10, 2019 approved the “Taiwan 5G Action Plan (2019-2022),” [19] with a total investment about NT$20.466 billion over a four-year period. The plan aims to build a 5G application and industrial innovation environment, and reshape Taiwan's mobile communication industry ecosystem, with its content planned around five themes, including "promoting 5G vertical application field demonstration", "building 5G innovation and application development environment," "completing 5G technology core and cybersecurity protection capabilities," "planning to release 5G frequency spectrums in line with overall interests" and "adjusting laws and regulations to create favorable environment for 5G development," and to promote industrial upgrading and transformation, as well as create the next wave of economic prosperity in Taiwan.
Secure, robust and reliable 5G systems are sufficient and requisite conditions for building an innovation ecosystem in digital countries. The third theme of the "Taiwan 5G Action Plan" is to "complete 5G technology core and cybersecurity protection capabilities," which is intended to advance the integration of applied science and technology by establishing advantageous core technologies, set up a 5G technology and test platform, and increase the market competitiveness of 5G industry, while drafting the overall national policies on 5G cybersecurity, building the cybersecurity protection mechanism of 5G homemade products, strengthening 5G critical infrastructure and operational cybersecurity protection capabilities, and promoting domestic suppliers to enter the international 5G reliable supply chain.
In terms of strengthening 5G critical infrastructure and operational cybersecurity protection capacities, the NCC has planned a four-year (2019-2022) "5G Network Cybersecurity Protection and Related Regulations Preparation Plan." In coordination with a 5G license issue in 2020, the agency in 2019 added/amended the 5G cybersecurity provisions of the Regulations for Administration of Mobile Broadband Businesses, making it mandatory for the winning bidder of the 5G frequency spectrum to incorporate the cybersecurity protection concept into the system design for system construction.
Upon commercial operation of 5G, the NCC will audit from time to time the implementation of the cybersecurity maintenance plan by telecom operators, so as to ensure and reinforce the cybersecurity protection system of Taiwan's 5G telecom network, and create an opportunity for the development of 5G homemade products with cybersecurity protection capability. In addition, the NCC will also face up to the fact that 5G technology standards continue to evolve, and the operators have different construction schedules and heterogeneous mobile networks coexist. Therefore, relevant regulations will continue to be completed from 2020 to 2022, and examples will be verified through cybersecurity function testing laboratories to ensure that cybersecurity protection functions of 5G networks keep pace with the times.
IV. Conclusion and Suggestion
As for emerging technologies, countries around the world are actively evaluating and constructing 5G systems and services. Taiwan boasts excellent industrial advantages in terms of semiconductors, ICT software and hardware, and high-quality talents, and thus makes a foundation for developing 5G. Furthermore, going with the importance of cybersecurity, it is necessary to pay more attention to planning and developing 5G cybersecurity technology.
It is clear that the development of cybersecurity is both a challenge and an opportunity for Taiwan. In order to implement the national policy objectives of "cybersecurity is national security" as well as "innovative economic development programs for a digital nation," and to response to the scientific and technological progress, and the demand for cybersecurity, key development direction is proposed to expedite the establishment of 5G cybersecurity protection.
Reference:
[1]Resilience, Deterrence and Defence: Building strong cybersecurity in Europe, European Commission, https://ec.europa.eu/digital-single-market/en/news/resilience-deterrence-and-defence-building-strong-cybersecurity-europe
[2]The draft Regulation of The European Parliament And of The Council on ENISA, the "EU Cybersecurity Agency", and repealing Regulation(EU)526/2013, and on Information and Communication Technology cybersecurity certification(''Cybersecurity Act'') was published in September 2017 to expand the rights and obligations of ENISA, which would make ENISA the EU's cybersecurity and information competent authority and the authority for critical infrastructure (information) facilities after the passage of the Act.
Regulation (EU) 2019/881 of the European Parliament and of the Council of 17 April 2019 on ENISA (the European Union Agency for Cybersecurity) and on information and communications technology cybersecurity certification and repealing Regulation (EU) No 526/2013 (Cybersecurity Act) (Text with EEA relevance), https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=uriserv:OJ.L_.2019.151.01.0015.01.ENG&toc=OJ:L:2019:151:TOC
[3]The EU cybersecurity certification framework, European Commission, https://ec.europa.eu/digital-single-market/en/eu-cybersecurity-certification-framework
[4]Cybersecurity Strategy(2018), DHS, https://www.dhs.gov/sites/default/files/publications/DHS-Cybersecurity-Strategy_1.pdf
[5]National Cyber Strategy of the United States of America(2018), The White House, https://www.whitehouse.gov/wp-content/uploads/2018/09/National-Cyber-Strategy.pdf
[6]THE WHITE HOUSE, Presidential Executive Order on Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure, The White House, https://www.whitehouse.gov/presidential-actions/presidential-executive-order-strengthening-cybersecurity-federal-networks-critical-infrastructure/
[7]DoD Digital Modernization Strategy, DoD, https://media.defense.gov/2019/Jul/12/2002156622/-1/-1/1/DOD-DIGITAL-MODERNIZATION-STRATEGY-2019.PDF
[8]National Cybersecurity Strategy, Public Safety Canada, https://www.publicsafety.gc.ca/cnt/rsrcs/pblctns/ntnl-cbr-scrt-strtg/index-en.aspx
[9]National Cross Sector Forum 2018-2020 Action Plan for Critical Infrastructure, Public Safety Canada, Public Safety Canada, https://www.publicsafety.gc.ca/cnt/rsrcs/pblctns/pln-crtcl-nfrstrctr-2018-20/index-en.aspx#a02
The action plan is a three-year program under Canada's2010 National Strategy for Critical Infrastructure (National Strategy) starting in 2010 for all phases.
[10]Enhancing Canada’s Critical Infrastructure Resilience to Insider Risk, Public Safety Canada, Public Safety Canada, https://www.publicsafety.gc.ca/cnt/rsrcs/pblctns/nhncng-crtcl-nfrstrctr/index-en.aspx
[11]Cybersecurity Act 2018, Singapore Statutes Online, https://sso.agc.gov.sg/Acts-Supp/9-2018/
[12]Cybersecurity Act, CSA, https://www.csa.gov.sg/legislation/cybersecurity-act
[13]Id.
[14]Cybersecurity Act Explanatory Statement, https://www.csa.gov.sg/~/media/csa/cybersecurity_bill/cybersecurity%20act%20-%20explanatory%20statement.pdf
[15]Australia’s Cybersecurity Strategy, https://cybersecuritystrategy.homeaffairs.gov.au/
What is the Government doing in cybersecurity, Ministers for the Department of Industry, Innovation and Science, https://www.industry.gov.au/data-and-publications/australias-tech-future/cyber-security/what-is-the-government-doing-in-cyber-security
[16]Australia’s International Cyber Engagement Strategy, Department of Foreign Affairs and Trade,https://www.dfat.gov.au/sites/default/files/DFAT%20AICES_AccPDF.pdf
[17]Essential Eight Explained, ACSC, https://www.cyber.gov.au/publications/essential-eight-explained
[18]Pacific Cybersecurity Operational Network(PaCSON), https://dfat.gov.au/international-relations/themes/cyber-affairs/cyber-cooperation-program/Pages/pacific-cyber-security-operational-network-pacson.aspx
Or Strengthening cybersecurity across the Pacific, ACSC, https://www.cyber.gov.au/news/pacific-islands
PaCSON is comprised of 15 members, including Australia, Fiji, Marshall Islands, New Zealand, Papua New Guinea, Samoa, and Solomon Islands.
[19]Taiwan 5G Action Plan, Executive Yuan,https://www.ey.gov.tw/Page/5A8A0CB5B41DA11E/087b4ed8-8c79-49f2-90c3-6fb22d740488
- Resilience, Deterrence and Defence: Building strong cybersecurity in Europe
- Regulation (EU) 2019/881 of the European Parliament and of the Council of 17 April 2019 on ENISA (the European Union Agency for Cybersecurity) and on information and communications technology cybersecurity certification and repealing Regulation (EU) No 526/2013 (Cybersecurity Act) (Text with EEA relevance)
- The EU cybersecurity certification framework
- Presidential Executive Order on Strengthening the Cybersecurity of Federal Networks and Critical Infrastructure
- National Cybersecurity Strategy
- National Cross Sector Forum 2018-2020 Action Plan for Critical Infrastructure
- Enhancing Canada’s Critical Infrastructure Resilience to Insider Risk
- Cybersecurity Act 2018
- Cybersecurity Act
- Australia’s Cybersecurity Strategy
- What is the Government doing in cybersecurity
- Essential Eight Explained
- Pacific Cybersecurity Operational Network(PaCSON)
- Strengthening cyber security across the Pacific
- Taiwan 5G Action Plan
In light of the influence on social security of Internet-related crime, in 2007 Taiwan passed the amendment to the Communication Protection and Inspection Act (CPIA) to update the articles relating to the surveillance of Internet-related crimes. Moreover, the notification obligator clause was added to the Child and Adolescent Sex Trade Prevention ACT (CASTPA), and the penalty for copyright infringement over the Internet was prescribed in the Copyright Act in order to stop Internet-related crimes. 1. Amendment to the CPIA On 15 June 2007, the legislature of Taiwan passed the amendment to the CPIA which was promulgated by the President of Republic of China on 11 July 2007. The amendment mainly concerns the update of the power of issuing surveillance warrants, the scope of emergency surveillance, the supervisory agencies of relevant surveillance activities, and the evidence power of illegal surveillance. The amendment will be brought into force in five months. Currently, a surveillance warrant is issued (1) by the district prosecutor following an application made by the police or based on his authority for cases under investigation; and (2) by the judge based on his power for cases on trial. According to Article 5.2 of the amended CPIA, for cases under investigation, the district prosecutor should record the details of surveillance in writing following the applications made by the judiciary police or based on his authority and should state the reasons and submit relevant documents before applying to the jurisdiction court for the issue of the surveillance warrant. The district prosecutor should approve and reply to the applications made by the judiciary police within 2 hours. For cases of greater complexity, the approval and reply time may be extended for another 2 hours with the consent of the chief district prosecutor. After receiving an application for a surveillance warrant from the district prosecutor, the jurisdiction court should approve and reply to the application within 24 hours. For cases on trial, a surveillance warrant should be issued by the judge based on his authority. Also, the judge may give appropriate instructions for the surveillance in the warrant. Moreover, if an application for a surveillance warrant is rejected by the court, the district prosecutor should make no objection in any form. In other words, the power of issuing a surveillance warrant for cases under investigation has been transferred from the district prosecutor to the judge. Furthermore, the law-enforcement authorities are given the right to initiate an “emergency surveillance” before application during the investigation of serious criminal cases according to Article 6 of the CPIA. In an investigation of serious criminal cases involving obstruction of voting, kidnapping, offence of the President and Vice President Election and Recall Act, the judiciary police may request the district prosecutor to orally notify the implemental authorities of an emergency surveillance. However, the district prosecutor should report to the jurisdiction court to apply for a make-up issue of the surveillance warrant within 24 hours. The district prosecutor’s office should appoint a responsible district prosecutor or a head district prosecutor as the emergency contact for cases involving emergency surveillance. The court should also assign a special window to take charge of the applications for surveillance warrants made by the district prosecutor, and should issue a make-up surveillance warrant within 48 hours of the acceptance of the application. Should the make-up surveillance warrant not be issued within 48 hours, the emergency surveillance should be terminated immediately. The district prosecutor, the court of law and agencies taking charge of the country’s intelligence work are responsible for the supervision of surveillance. According on Articles 12 and 16 of the amended CPIA, regulations governing the period and supervision of surveillance are summarized as follows: (1) The period of surveillance should not exceed 30 days for serious and emergency cases involving endangering national security or social order and blackmailing as in Article 5 of the CPIA; or for cases involving obstruction of voting, kidnapping and offence of the President and Vice President Election and Recall Act as in Article 6 of the CPIA. The responsibility of supervision is the district prosecutor's office for cases under investigation and the court of law for cases on a trial. (2) The period of surveillance should not exceed 1 year for collecting information of foreign powers or offshore opposing powers as in Article 7 of the CPIA. Intelligence authorities should send agents to supervise the electronic surveillance equipment or to the supplier of surveillance equipment to supervise the conditions of surveillance. Should continual surveillance be needed, the implemental agency should submit concrete reasons to make a second application for surveillance two days before the end of the first surveillance period. However, the surveillance should be terminated immediately when the chief of the intelligence agency believes that it is no need to continue the surveillance before the end of the surveillance period. Lastly, the exclusivity of the evidence power of information collected from illegal surveillance is added to Articles 5, 6, 7 and 32 of the amended CPIA. According to Articles 5 and 6, should the surveillance involve severe offence of regulations, the information or evidence collected from the surveillance will not be accepted as evidence in a judiciary investigation, a trial or relevant procedure. Additionally, according to Articles 7 and 32, information or evidence collected from illegal surveillance will not be accepted as evidence in a judiciary investigation, a trial or relevant procedure. The severity of the offence should be determined by the judge based on individual cases. 2. Amendment to the CASTPA Child pornography is easily distributed because of the advancement of Internet communication; and the prepubescent pornography market is expanding as a result. The legislature of Taiwan thus passed on 15 June 2007 the amendment to the CASTPA that was promulgated by the President of Republic of China on 4 July 2007. In the amendment, neighborhood heads, ISPs and telecommunication system providers are the obligator of notification, and “possessors” of child pornography are to be penalized. According to the explanatory statement of the act, child pornography is the permanent record of the abuse of the victims. This will inflict continual damage on the victims. Moreover, child pornography is considered a “serious child exploitation” all over the world. Therefore, there is an international understanding to penalize the possession of child pornography. Before the amendment, Article 28 of the statue simply penalizes people distributing and selling child pornography in the form of disc, videotape and printing. Those deliberately distributing, broadcasting and/or selling child pornography in the form of pictures, videotape, film, disc, electronic signal or other form will be penalized by imprisonment for a term of less than 2 years and with a fine of under NT$2 million. [In the amendment,] those deliberately distributing, broadcasting and/or selling child pornography are penalized and imprisonment for a term of less than 3 years and with a fine of under NT$5 million. While child pornography inflicts continual damage on the victims, Article 28.3 has been added to statute. According to this new Article, those in possession without a proper reason of pictures, films, videotapes, discs, electromagnetic recordings and/or other articles containing sexual intercourses or acts of indecency by people under 18 are to be penalized. In this case, the “possession” of child pornography is penalized. The penalization falls into two stages: competent authorities of municipalities and local counties and cities may order the offender to receive guidance education for 2-10 hours if he/she is detected possessing child pornography without a proper reason for the first time; if offenders are detected for the second time or more, they will be fined NT$20000 to NT$200000. The amendment also refers to the legislation in Canada and the Netherland to reduce the scope of “proper reasons for possession” to scientific study, education and for medical treatment purposes in order to protect prepubescent children from sexual exploitation. Moreover, the amendment has expanded the scope of the notification obligator by including ISPs and telecommunication system providers as the notification obligator. While the Internet and mobile phones are widely used by the public and prepubescent children often receive pornographic information via the chat rooms on the Internet and SMS, this will cause many side effects on prepubescent children in the absence of appropriate management and protection. According to the statistics provided by the Ministry of the Interior, about 300 prepubescent children are sexually assaulted every year from online dating. According to The Garden of Hope Foundation, 40% of sex trade with prepubescent girls found in Taipei County during 2003-5 was conducted over the Internet, and it was 100% for prepubescent boys. It is thus clear that the Internet has become a platform for distributing child pornography. ISPs and telecommunication system providers are included as the notification obligator in Article 9 of the amended statute. Therefore, if they do not notify the authorities in the knowledge of child pornography, they will be fined NT$6000-NT$30000 according to Article 36 of the statue. Therefore, neighborhood heads, ISPs and telecommunication system providers must notify the local competent authorities or authorities specified in Article 6 of any prepubescent children who engage or probably engage in the sex trade in their knowledge. This is designed in order to strengthen the notification and prevention functions and to effectively stop those who deliberately use chat rooms on the Internet and SMS to engage in true sex trade in the disguise of online dating. Though the scope of notification obligation has been expanded in the amendment to the CASTPA to strengthen the notification and prevention mechanisms of prepubescent children sex trade and to define the notification obligations of the supplier and provider of SMS, network chat rooms, BBS, blogs and e-news services, many problems arise as a result. First, when telecommunication system providers have the obligation of notification, they also need to submit relevant evidence. However, this may involve the infringement of privacy of communication. If telecommunication system providers must not commit illegal surveillance, they are unable to acknowledge the contents of communication of consumers. In this case, how can they notify any crime? On the other hand, though information over the Internet is open to the public, it is a tough question for law enforcement officers to provide solid evidence proving that the administrator of online chat rooms and blogs has failed to perform his obligation of notification. 3. Amendment to the Copyright Act The online music downloading service debate has become a heated issue in recent years for the following reasons: “to select only the songs I like”, “comprehensive repertoires”, and “convenience”. According to the Online Music Downloading Survey by the Secure Online Shopping Association (SOSA), 85% consumers have tried the online music downloading service, thus giving rise to the comprehensive online music downloading software and services. However, to attract consumers with files containing unlicensed music, video or other files and charge users of such services, some ISPs provide computer programs or technologies, e.g. point-to-point (P2P), for users to exchange such outlawed materials and charge users for such services. Such acts of making profit from copyright infringement has inflicted disputes in copyright infringement. For example, the IFPI’s accusation in 2003 of Kuro, a P2P platform provider, is the first convicted case of P2P music downloading service in Taiwan. Though the software supplied by Kuro is a neutral technology which is not illegal, Kuro recruited members and charged them membership fees for allowing them to illegally downloading, exchanging and reproducing a large amount of unlicensed copyrighted materials with such software and the platform services it supplies. Kuro also advertised that consumers can download tens of thousands of the latest popular songs with the Kuro software and even encouraged members to download them. Therefore, the court decided that Kuro and its members who have practically downloaded copyrighted music illegally are guilty of copyright infringement. On the other hand, ezPeer, another P2P downloading platform provider, was not found guilty of copyright infringement because no law was practiced at that time to prohibit or restrict the use of P2P software. Also, as a transfer platform, ezPeer offers comprehensive functions and it is thus not a tool for committing crime. Even some users transfer or download unlicensed copyrighted materials with this tool, there is possibility for the non-liability reasonable use. Moreover, ISPs have no filtering obligations in the Copyright Act of the ROC. Therefore, even consumers may use the services for illegal activities, P2P service providers are not an accomplice. Therefore, to define the liabilities of P2P platform providers, the legislature of Taiwan passed on 14 June 2007 the amendment to the Copyright Act to include P2P software providers in governance of the act. In the future, platform providers will be prohibited by the Copyright Act from charging members for unlicensed activities. New objects of copyright infringement are added to the amendment, and the amendment includes the addition of Article 87.1.7, 87.1.2, and 97.1; and the revision of Article 93.4. According to Article 87.1.7, attempt to allow the public to openly transfer or reproduce works of others without prior consent or licensing from the owner is copyright infringement, and supply of computer programs and/or technologies that can be used for public transfer and/or reproduction of such for the purpose of making profits is deemed as copyright infringement. As the supplier of computer programs and/or technologies is the focus of this article, behaviors categorized based on this article must also meet the following requirements: (1) attempt to allow the public to download and/or transfer over the Internet copyrighted materials without prior consent or licensing of the copyright owner; (2) the act of supply of computer programs and/or technologies; (3) and making profits from such behaviors. In other words, the focus of the amendment is to prohibit providers by written law from supplying computer programs and/or technologies for users to transfer and/or exchange unlicensed music, video and/or other copyrighted materials and from charging users or making profits from such services. However, the amendment has adopted the principle of technology neutrality and specifies that P2P software providers will only be penalized when they have the act of making profit and the intention of copyright infringement in order not to prevent technological development and to save ISPs from breaking the law all the time. As the “intention” of copyright infringement is the criterion of judgment, Article 87.2 is added to the Copyright Act in the present amendment. According to this article, whether or not the doer instigates, guides or incites in advertisements or other active actions the public to use the computer programs and/or other technologies it supplies to commit copyright infringement is the criterion for determining the “intention” of copyright infringement. Also, the court will determine with severity whether or not the advertisements or other active actions are ready for instigating, guiding or inciting the public use the computer programs and/or other technologies the doer supplies to commit copyright infringement. In general, when providers offer services, such as web photo albums, BBS, instant messengers, auctions, web disks and online discussions, it is not their initial intention to supply software and/or technologies for users to illegally download and/or transfer the copyrighted materials of others, nor do they encourage, instigate, guide, incite and/or convince users to commit copyright infringement. Even such software can be used for transferring and/or distributing unlicensed copyrighted materials, providers must not be restricted, and it should be the users who take the liability of copyright infringement. After the enactment of the amendment, providers who make profit from supplying software for others to distribute unlicensed copyrighted materials and encourage users to exchange such materials with the software are to be penalized by imprisonment for a term of less than 2 years, community service, or fined, or penalty together with a find of under NT$500000 according to Article 93. Moreover, by adding Article 97.1, the competent authorities are entitled to order ISPs to shutdown or close the business when they are convicted for the abovementioned offences and refuse to stop such illegal acts after being determined for “severe copyright infringement” and “severely injury of the benefits of the copyright owner”. After this amendment of the Copyright Act, service providers can no longer use the excuse “we simply provide a service platform and have no right to check the behavior of consumers” as an escape of their liabilities. In fact, P2P service providers who charge users monthly fees for the P2P software, such as Kuro and ezPeer, have already signed licensing agreements with music companies before the enactment of this amendment. Therefore, the music they provide for users to download is no more unlicensed copyrighted materials. Therefore, the amendment has certain effect on improving copyright protection.
To establish a trusted foundation for sports data compliance, the Sports Data Altruism Service releases the Sports Data Altruism Service Personal Data Assessment Legal Compliance HandbookTo establish a trusted foundation for sports data compliance, the Sports Data Altruism Service releases the Sports Data Altruism Service Personal Data Assessment Legal Compliance Handbook 2024/05/15 I. Introduction The Sports Data Altruism Service aims to construct a blueprint for the development of sports and technology, to promote practical applications for sports scientific research results, to drive industry development, and to establish a sports data innovation ecosystem. This will be achieved through multi-ministerial/multi-agency value-added applications for sports data, multidisciplinary upgrading and transformation of sports technology, digital empowerment to establish a sports technology ecosystem, and public-private collaboration efforts. The Sports Data Altruism Service aims to build a legal compliance platform, and to reinforce the trust foundation for legally-compliant sports data operations, all while balancing privacy protection and public interest. In pursuit of these ends, the Sports Data Altruism Service draws upon international data governance practices and trends, as well as current industry practices. It aims to develop guidelines and regulations that consider the value of sports data applications and apply them to data legal compliance operations for sports venues. The Service is also intended to help operators in the sports field maintain personal data protections and reasonable use. Consequently, in August 2023, the Sports Data Altruism Service released the Sports Data Altruism Service Personal Data Assessment Legal Compliance Handbook. For entities seeking to become Sports Data Altruism Service data providers, the Handbook explains the related regulations and provides important things to watch out for. II. Structure of the Sports Data Altruism Service Personal Data Assessment Legal Compliance Handbook The Handbook is divided into three sections: A. Requirements for joining the Sports Data Altruism Service: Before starting with the Sports Data Altruism Service, users must read and agree to the service’s Privacy Policy, Terms of Service, Notification Regarding Personal Data Collection and Personal Data Provision Agreement, and other important platform information. The Privacy Policy explains how the platform collects, uses, and protects the information that users provide. If you wish to become a data provider or data user, the Terms of Service will explain what you need to comply with to do so. And if you decide to become a data provider or data user, you must register on this platform and must sign the "Notification and Letter of Consent for Collection, Processing, and Use of Personal Data" to state your agreement to provide your data to the platform. B. Personal data subject rights protection mechanism for sports venue operators (data providers): After becoming a Sports Data Altruism Service data provider, to lawfully obtain the personal sports data, the data provider must submit the Points of Note When Connecting to the Sports Data Altruism Service and Personal Sports Data Provision Agreement. This form, submitted in either paper or online format, must include a signature from the person whose personal sports data is to be used. When a data subject needs to correct their personal data or no longer wishes to provide their data to the Sports Data Altruism Service, the data provider must provide the Exercise of Data Subject Rights Application Form. After the data subject submits the application, the sports venue operator must verify whether the data has been processed to the extent that it cannot be used to identify a specific individual. In accordance with Article 4 of the Points of Note When Connecting to the "Notice of Connection to the Sports Data Altruism Service Platform and Consent Form for Provision of Personal Sports Data", data that can no longer identify specific data subjects is no longer considered personal data, and is not subject to exercising of data subject rights, nor is it subject to deletion of statistical or analytical results based on such data. If the data has not been anonymized, the operator must remove the data subject from the list uploaded to the platform and delete any unprocessed sports data. They must also retain records of the deletion and notify the data subject. Source: Sports Data Altruism Service Personal Data Assessment Legal Compliance Handbook Figure 1 Data Subject Rights Exercise Mechanism for Sports Venue Operators C. Data protection management process for sports venue operators (data providers): To assist sports venue operators in complying with personal data protection requirements, the Sports Data Altruism Service provides a personal data protection self-assessment tool. After an operator becomes a Sports Data Altruism Service data provider, they must assess their compliance with data protection laws by completing the Self-Assessment Form for Personal Data Protection in Collecting Public Sports Data by Sports Venue Operators (Data Providers). This helps operators understand the importance of personal data protection and establish a robust personal data protection management system, to achieve both data protection and reasonable usage. The Self-Assessment Form for Personal Data Protection in Collecting Public Sports Data by Sports Venue Operators (Data Providers) is designed in accordance with the regulations of the Personal Data Protection Act and its enforcement rules. It includes 20 assessments in 10 major categories. When filling out the self-assessment form, the operator must provide the name of the self-assessment venue, the name of the person filling out the form, and the date. The form has to be completed based on the personal characteristic data and sports data that is to be uploaded to the Sports Data Altruism Service. However, not every assessment is mandatory. The form requires considering the operator’s actual situation to review the current practices related to personal data protection and management, then conducting the self-assessment based on this. For more detailed information about the Sports Data Altruism Service Personal Data Assessment Legal Compliance Handbook, please visit the Sports Data Altruism Service website (https://www.data-sports.tw/#/SportData/Landing?redirect=%2FDashboard).
Implementing Information Security to Protect Individuals' PrivacyThe development of new technology is bound to have both positive and negative effects. However, when a new technology is first introduced, it is common for insufficient attention to be paid to its negative aspects, either because there has not been time to accumulate sufficient experience in using it or because users are blinded by the potential benefits. It is only later, when the technology begins to be abused, that people wake up to the potential dangers. The evolution of computers and the Internet is a classic example of this phenomenon. While the rapid development of information technology has helped to stimulate the flow of information in every corner of society, cyberspace has also become the setting for a wide range of criminal activities. In many cases, countries' existing legal and regulatory frameworks have proved inadequate to cope with the threat posed by the various forms of unauthorized access. A variety of forms of cyber-crime have developed, including denial-of-service attacks, unauthorized accessing of databases, phishing, identity theft and online fraud or intimidation. Cyber-crime may involve making unauthorized use of individuals' personal information, stealing companies' confidential business information or selling state secrets; these new types of crime thus affect every level of society. The effects can be catastrophic, hence the growing importance is now being attached to information security, including both the establishment of effective management mechanisms to prevent cyber-crime from occurring in the first place and the development of the capabilities needed to detect such crime when it occurs. Recognizing the need to plug the gaps in the existing legal and regulatory framework in the face of cyber-crime, countries all over the world are working on the formulation of new legislation, and Taiwan is no exception. The following sections will discuss the key developments in the laws and regulations governing information security in Taiwan in recent years. I. The Convention on Cyber-crime and Chapter 36 of Taiwan’s Criminal Code (offences relating to the abuse of computers) Today, governments throughout the world are formulating measures to combat criminal activity that makes use of the Internet (cyber-crime). In many cases these measures are based on the Convention on Cyber-crime announced by the European Commission on November 23, 2001, and which came into effect on July 1, 2004. This convention is the first international agreement to be established specifically to combat cyber-crime. Its contents include discussion of the various types of cyber-crime, regulations governing the obtaining of electronic evidence, provisions for mutual assistance between nations in judicial matters with respect to cyber-crime and measures to encourage multilateral collaboration. The European Commission asked all signatory nations to revise their own national laws so that they conform to the provisions of the Convention, with the aim of establishing a unified international framework for combating cyber-crime. Responding to the international trend towards the enactment of legislation to fight cyber-crime and to eliminate any loopholes in Taiwanese law that might result in Taiwan becoming a haven for cyber-criminals, on June 25, 2003 the Taiwanese government added a new chapter, Chapter 36 (Offences Relating to the abuse of Computers) to Taiwan's Criminal Code. It contains six articles covering four types of crime: unauthorized access (Article 358), the unauthorized acquisition, deletion or titleeration of electromagnetic records (Article 359), unauthorized use of or interference with a computer system (Article 360) and creating computer programs specifically for the perpetration of a crime (Article 362). Article 361 specifies that more severe punishment should be imposed in the case of violations carried out against the computers or other equipment of a public service organization, and Article 363 states that the provisions of Articles 358–360 shall apply only after prosecution is instituted upon complaint. These new articles provide a clear legal basis for the punishment of common types of cyber-crime such as unauthorized access by hackers, the spreading of computer viruses and the use of Trojan horse programs. In formulating these articles, reference was made to the categorization of cyber-crimes used in the Convention on Cyber-crime and to the suggestions for revision of national laws put forward there. Article 36 is thus in broad conformity with current international practice in this regard and can be expected to achieve significant results in terms of combating cyber-crime. II. The authority of law enforcement to get evidence and ISPs liability In its discussion of the securing of electromagnetic records by law enforcement agencies, the Convention on Cyber-crime notes that such securing of records falls into two broad categories: immediate access and non-immediate access. Immediate access includes the monitoring of communications by law enforcement agencies, non-immediate access relates mainly to the data retention obligations imposed on Internet Service Providers (ISPs). As regards the regulatory framework for the monitoring of communications, Communications Protection and Surveillance Act came into effect in Taiwan on July 16, 1999. According to its provisions, monitoring of communications may only be implemented when it is deemed necessary to protect national security or to maintain social order. Warrants for such surveillance may only be issued if the content of the communications is related to a threat to national security or to the maintenance of social order. Furthermore, the crime in question must be a serious one. In principle, the period for which surveillance is implemented should not exceed 30 days. These restrictions reflect the government’s determination to ensure that citizens' right to privacy is protected. While the Internet is an environment conducive to the maintenance of anonymity, electromagnetic records are easy to erase. Effective investigation of cyber-crime requires automatic recording of communications by the equipment used to transmit the messages, that is to say, it requires the retention of historic data. As regards the extent to which companies are required to collaborate with law enforcement agencies and the conditions applying to the making available of electromagnetic records, these issues relate to the public's right to privacy, and the law in this area needs to be very clear and precise. For the most part, data retention obligations are laid down in Taiwan’s Telecommunications Act. In Taiwan ISPs are classed as "Type II Telecommunications Operators". Article 27 of the Administrative Regulations on Type II Telecommunications Businesses stipulates that Type II telecommunications operators may be required to confirm the existence of, and provide the contents of, customers' communications for the purpose of investigation or collection of evidence upon request in accordance with the requirements of the law. ISPs are required to retain, for a period of between 1 and 6 months, data relating to the account number of subscribers, the times and dates of communications, the times at which subscribers logged on and off, free e-mail accounts, the IP addresses used when applying for Web space and the time and date when such applications were made, the IP address used to make postings on message boards and newsgroups, the time and date when such postings were made and subscribers' e-mail communications records. If a Type II telecommunications operator violates these provisions, he may be fined between NT$200,000 and NT$1 million and be required to remedy the situation within a specified time limit in accordance with Paragraph 2 of Article 64 of the Telecommunications Law. If he fails to remedy the situation within the specified time limit, his license may be revoked. III. The Legal Framework for Personal Data Protection titlehough, as outlined above, some revisions have already been made to the legal framework governing information security, there are still many areas which need to be reviewed. One of the most important is the protection of personal information. Following the explosive growth of the Internet, customer-related information is being processed by computers on a large scale in many different industries. With so many companies collaborating with other firms or adopting new marketing methods, the value and importance of personal information is being reassessed. The dramatic increase in the number of online scams in Taiwan in recent years has made the protection of privacy a focus of attention. The existing Computer-processed Personal Data Protection Law, drawn up to target specific industries, does not really provide adequate protection. A new Personal Data Protection Act, drawn up with reference to the European Union’s Directive (95/46/EC) on the Protection of Individuals with regard to the Processing of Personal Data and on the Free Movement of Such Data and the personal information protection legislation adopted in the USA and Japan, has already been submitted to the Legislative Yuan for deliberation. The key differences between this new Act and the existing Computer-processed Personal Data Protection Law are as follows. Protection is no longer industry-specific, it now applies to both natural and juristic persons and to both public and private agencies. The scope of protection has been expanded to include hard copies of documents containing personal information, and five new types of "sensitive information" – information relating to criminal records, medical examinations, medical records, sexual history and genetic information – have been added. Special restrictions apply to the collection and processing of these types of data. The Personal Data Protection Act also imposes stricter requirements on public and private agencies with regard to the protection of individuals' personal data. For example, agencies must formulate personal data protection plans and measures for dealing with personal data once those data are no longer needed for business purposes. If an agency discovers that an individual's personal data have been stolen, leaked, titleered or violated in any way, they are required to notify by telephone or letter the agency responsible for notifying the individual concerned as soon as possible. If these provisions are violated, the agency's responsible person will be liable for administrative punishment. The new Act also gives regulatory authorities greater powers to undertaking auditing in this area, makes provision for class action suits and increases the amount of compensation to be paid to victims. It is expected that these mechanisms will help boost awareness of the importance of information security in all sectors, thereby helping to ensure better protection for the public's personal information. IV. Management of Unsolicited Commercial E-Mail The widespread utilization of e-mail has created a brand new marketing channel, so that e-mail can fairly be described as one of the most important "killer applications" to which the Internet has given rise. Today, spamming is causing serious problems for both e-mail users and ISPs. E-mail users are concerned about their privacy being violated and about having their e-mail box stuffed full of junk e-mail. Spamming also ties up bandwidth which could be used for other purposes, and Distributed Denial of Service Attacks (DDOS) can make it difficult for ISPs to provide normal service to their customers. Governments throughout the world have begun to consider whether anti-spamming legislation may be necessary. In Taiwan draft legislation of this type has already been submitted to the Legislative Yuan. Taiwan's Anti-SPAM Act was drawn up with reference to the USA's CAN-SPAM Act of 2003, Japan's Law on Regulation of Transmission of Specified Electronic Mail, Australia's SPAM Act and the UK's Privacy and Electronic Communications (EC Directive) Regulations 2003. The draft SPAM Act contains 13 articles, with an emphasis on self-regulation, technology filtering and provision for seeking compensation through civil action. The Act provides for the use of an "opt-out" mechanism to regulate the behavior of e-mail senders, with the following obligations to be imposed on them. (1) The sender must specify in the "Subject" field of the e-mail whether it is a "business communication" or "advertising" to facilitate filtering by ISPs and to make clear to the recipient what type it is. (2) The sender must provide accurate information, including header, information on the sender's identity and the sender's e-mail address. (3) E-mails may not be sent if the sender knows or could be expected to know that the intended recipient has already expressed a wish not to receive e-mail from this source. E-mails may also not be sent if the sender knows or could be expected to know that the information in the "Subject" field is inaccurate or misleading. If the sender continues to send e-mails after the recipient has expressed a clear wish not to receive any more from the sender or if the sender falsifies the "Subject" or header information, then the sender may be required to pay compensation to the recipient at a rate of NT$500–2,000 per person per e-mail. With regard to the widespread practice whereby companies or advertising agencies commission third parties to send junk e-mail on their behalf, in cases where the commissioning party knows or could be expected to know that e-mail is being sent in violation of the above regulations, the commissioning party shall be held jointly liable with the party sending the e-mail. Through the implementation of this new law, the government hopes to establish a first-class Internet environment in Taiwan, putting an end to the current situation whereby large numbers of businesses are engaged in spamming. V. Conclusions Security is the biggest single factor affecting the implementation of e-government initiatives, e-business application adoption and Internet user confidence. Most people associate information security only with the purchasing of security hardware or software and the setting up of firewalls. While these products can indeed help to make the online environment more secure, Internet users should not allow themselves to be lulled into thinking that buying these products will in and of itself be sufficient to ensure security. "Security" is a fluid concept. Over time, the level of security that even a high-end product can provide will deteriorate; the fact that your system is secure now does not guarantee that it will remain secure in the future. Evidence that this is true is provided by the damage that is constantly being caused by viruses, by the need to constantly update security products and by the shift in emphasis away from virus prevention and firewalls towards preventing "backdoor" attacks and towards proactive intrusion detection. Furthermore, the information security risks that companies and organizations have to deal with are not limited to external threats; poor internal management may result in employees selling or leaking customer data or other company data, which can cause serious damage to the organization. Examination of information security theory and practice in Taiwan and overseas suggests that the establishment of effective information security measures embraces four main areas: the detection of cyber-crime, development of new information security technologies and formulation of standards, education and management of computer users and regulatory and policy issues. The most important of these is the education and management of computer users. Detection of cyber-crime is the next most important, while development of new technologies and standard setting and the regulatory and policy aspects play a supporting role. To create a genuinely secure online environment, attention must be paid to all of these. Today governments throughout the world are formulating new legislation to plug the gaps in the regulatory framework governing the online environment. Given the need to let the market mechanism operate freely and to refrain from measures that might retard industrial development, government interference in the Internet, with the exception of crime prevention activity, has generally been viewed as a last resort. Currently the government in Taiwan is still focusing mainly on self-regulation by Internet service providers and other types of business enterprise, and the government's role is still largely confined to formulating standards and assisting with the development of new security products. The area on which both the government and the private sector will need to concentrate in the future is educating and ensuring effective management of computer users.
Research on the Introduction of Privacy Protection Management Mechanisms and Data Value-Added Services into Communications Enterprises in 2020Research on the Introduction of Privacy Protection Management Mechanisms and Data Value-Added Services into Communications Enterprises in 2020 2021/12/09 I. Introduction The global economy is shifting away from traditional economic models towards an emerging digital era as technology advancement and new applications are introduced. The rapidly changing digital age has led to a gradual transformation in the way digital technology is used in the industry, thereby driving the overall growth of the global digital economy. The digital economy is driven by "data," and how data is used, its purpose, risks and regulation are all inextricably intertwined with industrial development and application, as is the case for the communications industry. As such, while the free circulation of data has become central to international free trade and economic operations, it is not only conducive to the promotion of transnational business and economic and trade interactions, but also fraught with worry and concern over how to ensure the protection and security of personal data and privacy. As a result, the issue of how to adapt the data risk control mechanism and related complementary measures so that they can be applied to the industry and comply with regulatory requirements has become a global reality that must be actively addressed. As far as Taiwan is concerned, when considering how to cope with industry needs, there is a pressing need to strike a balance between personal data and international regulatory requirements, and to expedite the legitimate utilization of personal data protection and data value-added service in the sector in an effort to facilitate the development of the digital economy. II. Recommendations on Data Governance and Innovative Application Planning. According to the aforementioned international data strategies and strategies for innovative data applications, the development of the data economy as a whole is driven by the formulation of overall superior policies, with a view to fully utilizing the potential value of data and building a vibrant ecosystem suited for innovative data applications. With the outbreak of COVID-19 this year, the application of data will be crucial in the post-pandemic era. It is also observed that data applications are gradually moving towards cross-boundary sharing and reuse, and empowerment of data subjects, and therefore, in light of the above observations and findings, we offer recommendations on data governance and innovative application planning. First, as for the establishment of a ministry and mechanism for data application and communication, since there is no single dedicated authority in Taiwan, and the formation of a ministry for science and technology development is now under intense discussion, data application may become an important function of the ministry, so we have to consider an authority for data application and communication. Further, there is currently no sandbox mechanism for data application in Taiwan. Reference should be made to the British data communication mechanism for providing legal advice and consultation sought on data application regulation. Second, with regard to the formulation of regulations and amendments to existing laws relating to data applications, the most noteworthy is the EU Data Governance Act 2021. Taiwan does not have a complete and appropriate legal framework for data application, except for the Freedom of Government Information Law, the Personal Data Protection Act (PDPA) and the relevant laws and regulations distributed in various fields, and the nation is currently seeking an adequacy decision from the EU, and therefore our PDPA needs to be amended accordingly, yet no progress has been made at this stage. Consequently, a comprehensive strategy should be developed by taking into account both the formulation of the basic data application regulations and the amendments to the current PDPA, in order to achieve long-term data governance and application and sharing. Lastly, in terms of the incorporation of the concept of data empowerment and the design of the mechanism, the international trend moves towards data empowerment to give data subjects more control over their data. The Financial Supervisory Commission (FSC) of Taiwan has also incorporated this idea in its open banking, so has the National Development Council’s (NDC) MyData program. As such, it is suggested that the government should provide guidelines or devise the relevant system, or even make reference to the Japanese data bank mechanism regarding the establishment of intermediaries to assist consumers in managing their data, which could be used as a reference for the design of the mechanism in the future. III. Accountability for and Management of Data Use in Enterprises Among the countries studied regulation of Singapore and Taiwan are similar and have adopted the development of digital economy as their main economic strategy, but Singapore has been more proactive than Taiwan in the design of the legal system to facilitate the use of data. Therefore, with regard to the control of data use in businesses by the competent authorities, this Project, by looking at the amendment to the Singaporean PDPA, aims to reinforce the regulation of the accountability system and the operation of the existing series of guidelines. From the changes in Singapore's PDPA, it can be observed that the competent authorities can refer to the practices of enterprises in the use of data. First of all, the existing regulations in Taiwan tend to have more about compliance than accountability, with emphasis being placed on data security maintenance and compliance with the PDPA. For instance, Taiwan’s “Regulations Governing Security Measures of the Personal Information File for Non-government Entities Designated by National Communications Commission” focus on following the law on the use of personal data. Nonetheless, the so-called accountability means that the competent authorities must oversee the implementation of data protection measures and policies of enterprises, not just pro forma compliance with the letter of the law. The second observation is that Singapore is quite proactive in addressing the need for data use in the development of its digital economy by making an exception to innovative uses regarding informed consent. The inclusion of data portability also represents a heightened control of the data subject. These amendments are all related to Singapore's policy of actively developing its smart nation initiative and signify a more proactive approach by the authorities in monitoring the use of data by businesses. Taiwan needs to be more open and precise in regulating the use of data for the development of its digital economy. Finally, there is increased flexibility in enforcement, as authorities can resolve disputes between subjects over data use more quickly through the introduction of mediation or other alternative dispute resolution (ADR) mechanisms. Meanwhile, the Personal Data Protection Commission (PDPC) has developed industry-specific consultation guidelines, recognizing that there may be specific issues for different industries. The PDPC noted that these guidelines are based on the partnerships, consultations and feedback associated with the relevant industries, and close collaboration with the industry's authorities of target businesses. IV. Conclusion Despite the lack of a dedicated authority for personal data protection, Taiwan can first build a cross-industry coordination and communication platform, and then collaborate across ministries to primary integrate standards in personal data protection to facilitate the needs of industrial innovation in the digital economy.
- Impact of Government Organizational Reform to Scientific Research Legal System and Response Thereto (1) – For Example, The Finnish Innovation Fund (“SITRA”)
- The Demand of Intellectual Property Management for Taiwanese Enterprises
- Blockchain in Intellectual Property Protection
- Impact of Government Organizational Reform to Research Legal System and Response Thereto (2) – Observation of the Swiss Research Innovation System
- Recent Federal Decisions and Emerging Trends in U.S. Defend Trade Secrets Act Litigation
- The effective and innovative way to use the spectrum: focus on the development of the "interleaved/white space"
- Copyright Ownership for Outputs by Artificial Intelligence
- Impact of Government Organizational Reform to Research Legal System and Response Thereto (2) – Observation of the Swiss Research Innovation System

